Authentification Guide — Two authenticators

The Definitive Guide to 2 Factor Authentication - by Arsen
How to set up the Two-Step Authorization (Google Authenticator). – Gaijin Support

Browser-in-the-Browser Attack Makes Phishing Nearly Invisible - vulnerability database
Types of two-factor authentication, pros and cons: SMS, authenticator apps, YubiKey
How to set up the Two-Step Authorization (Google Authenticator). – Gaijin Support

A guide to common types of two-factor authentication

Types of two-factor authentication, pros and cons: SMS, authenticator apps, YubiKey
WebAuthn Readiness Checklist
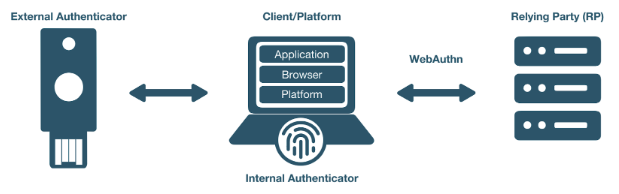
WebAuthn Developer Guide
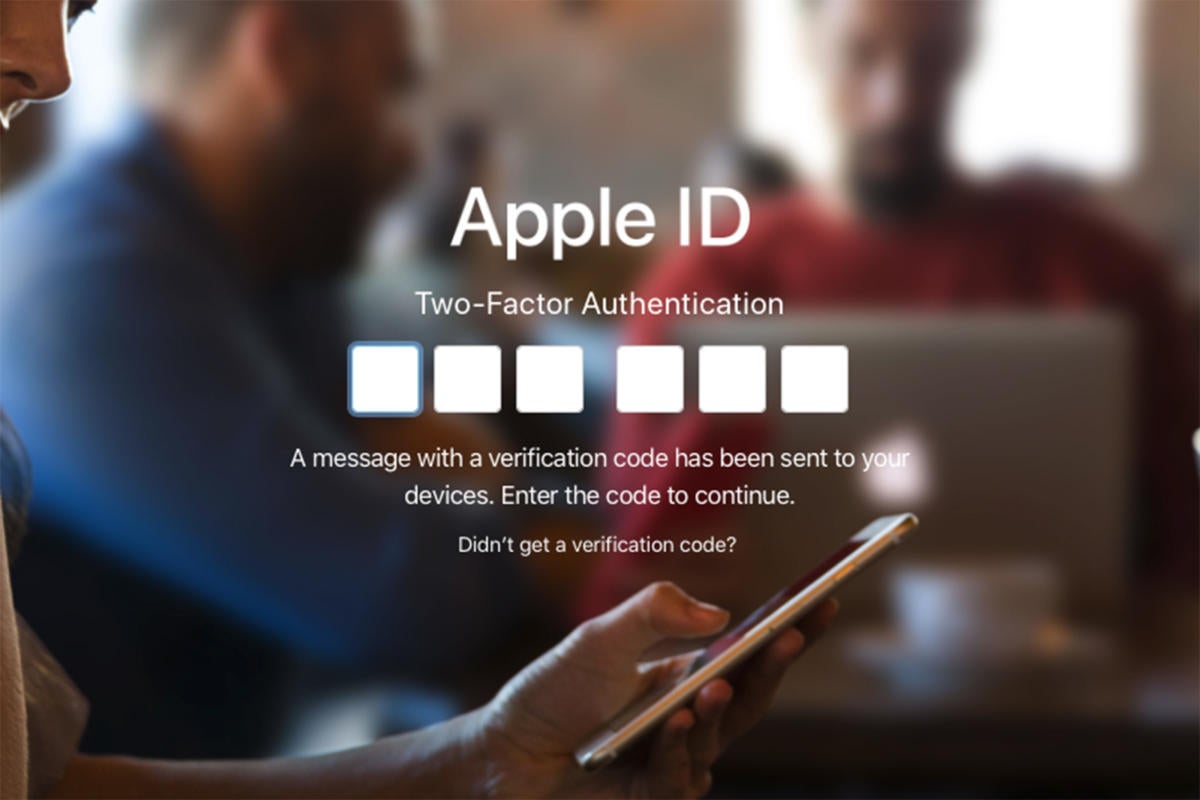
Two-factor authentication explained: How to choose the right level of security for every account
Types of two-factor authentication, pros and cons: SMS, authenticator apps, YubiKey
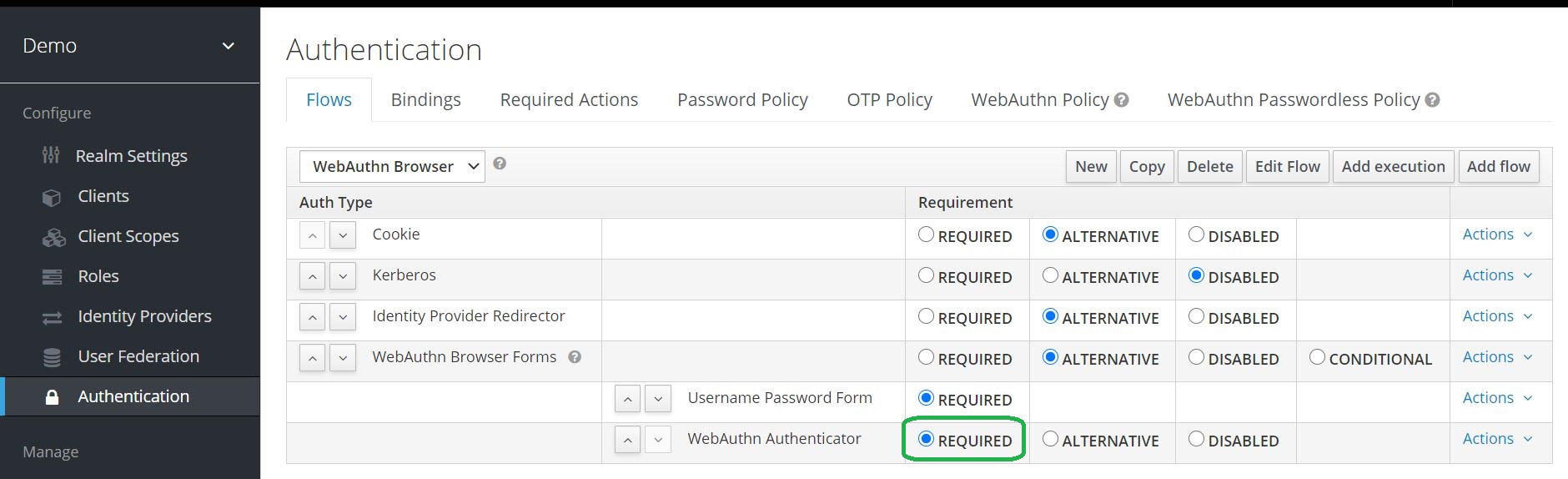
Two-Factor Authentication with Keycloak WebAuth · Ultimate Security Professional Blog
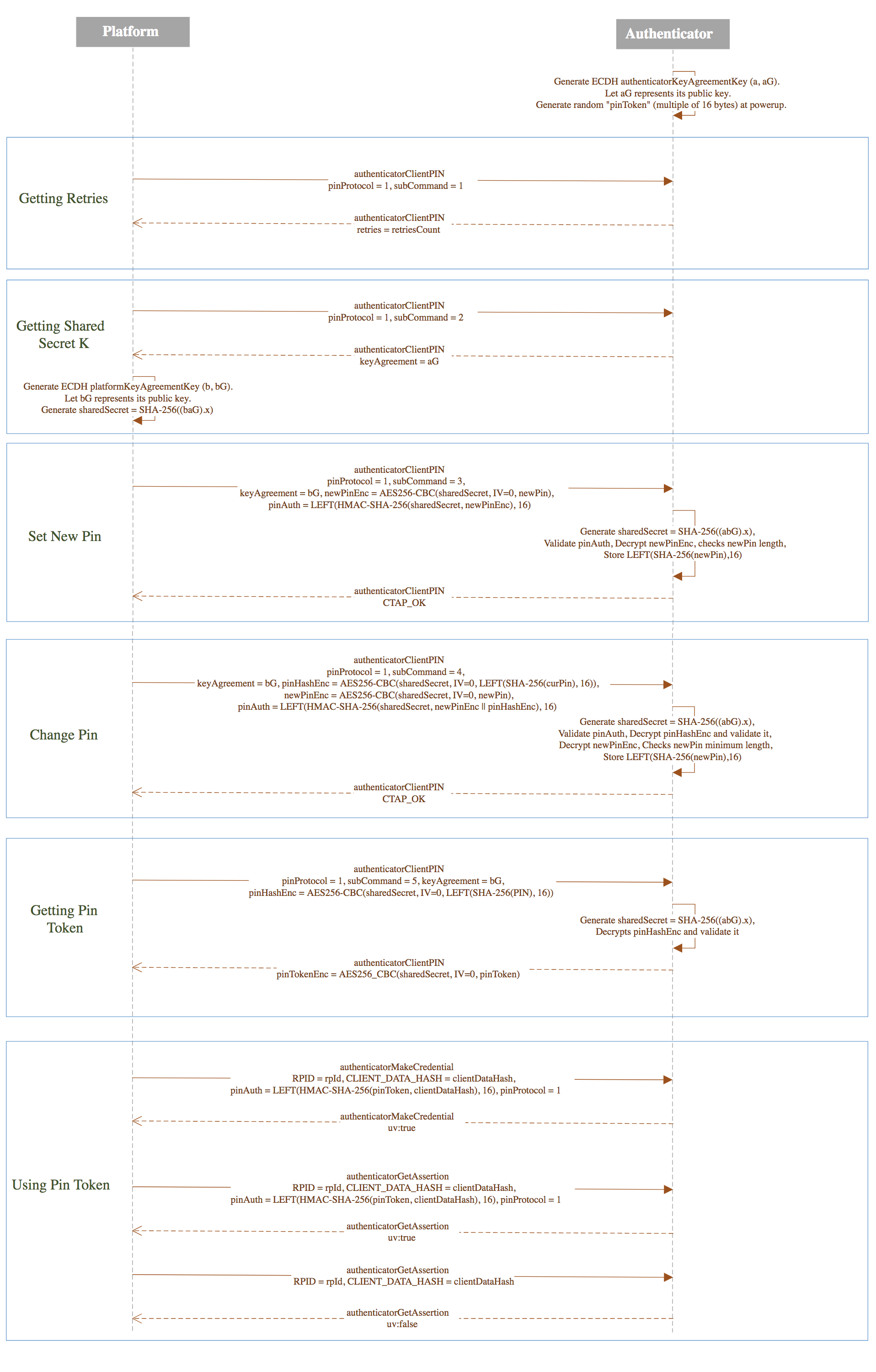
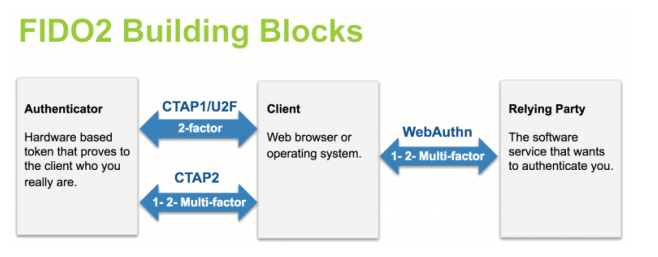
Client to Authenticator Protocol (CTAP)
Authentification Guide — Two authenticators
- Best Price $ 1270.00. Good quality and value when compared to ratchadalawfirm.com similar items.
- Seller - 781+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-
Louis Vuitton Clapton 4-Way Bag - backpack, satchel, crossbody, shoulder bag. $2000. With box and dust bag. DC Shop online or in…
Buy It Now 10d 17h -

Vintage Louis Vuitton Brown Monogram Fold Over Organizer Crossbody Bag
Buy It Now 7d 5h -

Louis Vuitton LV Volt Mesh Necklace
Buy It Now 6d 14h -

White Louis Vuitton Damier Azur Eva Crossbody Bag – Designer Revival
Buy It Now 3d 23h -

Louis Vuitton Petit Sac Plat Sunrise Pastel in Coated Canvas/Leather with Gold-tone - US
Buy It Now 4d 23h -
Minion Collection - PRELOVED BRANDED Bag ❤LOUIS VUITTON BAG❤ Good as new condition #Minion Collection disclaimer MINION COLLECTION is not associated or affialiated LOUIS VUITTON.
Buy It Now 12d 10h -

Introducing Louis Vuitton Brittany
Buy It Now 13d 5h -

Louis Vuitton Amarante Monogram Vernis Melrose Avenue Bag
Buy It Now 6d 19h -

Netflix hit 'Emily in Paris' draws cast to French capital for global premiere
Buy It Now 17d 13h -
:max_bytes(150000):strip_icc():focal(719x0:721x2)/paul-forman-121922-6-5d8e18bccdac4124aa3d3a3e4ddac820.jpg)
Who is Paul Forman from 'Emily in Paris' Season 3?
Buy It Now 9d 7h -

Unzipped Green Camo by New Vintage Handbags
Buy It Now 27d 23h -

Yayoi Kusama for Louis Vuitton
Buy It Now 16d 20h -

DIOR Men x BIRKENSTOCK, ode to nature and gardening, two of
Buy It Now 10d 21h -

Christian Louboutin Black/White Leather Rantus High Top Sneakers
Buy It Now 4d 9h -

Louis Vuitton 2006 Pink Monogram Denim GM Bag · INTO
Buy It Now 28d 21h -
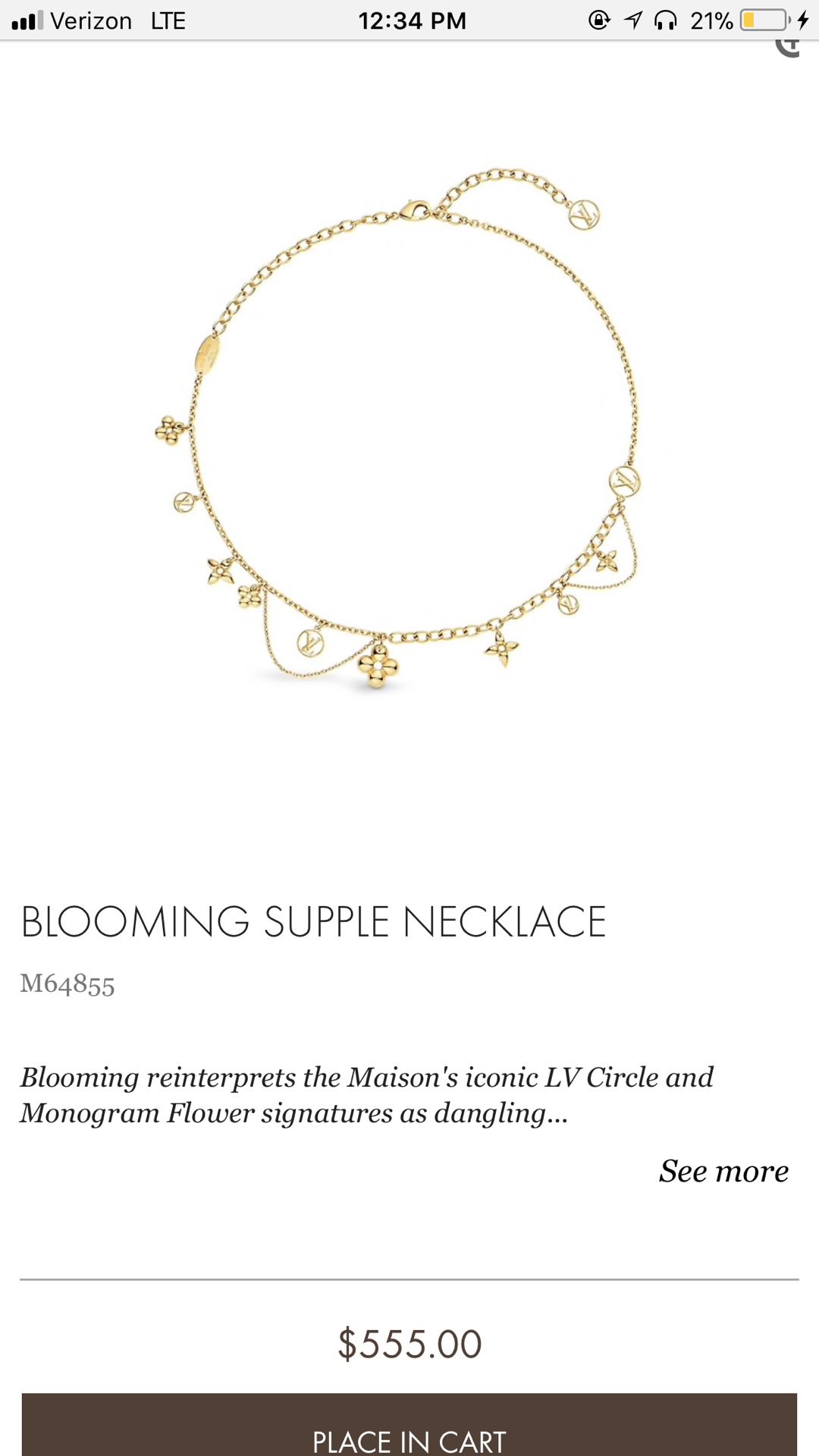
Louis Vuitton Blooming Supple Necklace for Sale in Las Vegas, NV - OfferUp
Buy It Now 28d 23h -

Louis Vuitton Mens Blue Monogram Silk All Over Logo Classic Neck
Buy It Now 18d 7h -

Nicky Hilton Out in Los Angeles September 19, 2010 – Star Style
Buy It Now 9d 18h -

Calvin Klein Jeans store, Melbourne » Retail Design Blog
Buy It Now 22d 17h -

Nike Air Max 1 CLOT Kiss of Death | Size 5, Sneaker
Buy It Now 28d 5h -

This Small Kira Shoulder Bag From Tory Burch is Perfect for Her
Buy It Now 8d 13h -

Bottega Veneta Green Mini Pouch Clutch
Buy It Now 21d 21h -

8 Best Louis vuitton slippers ideas louis vuitton shoes, vuitton, louis vuitton handbags
Buy It Now 2d 16h -

Louis Vuitton Maxi Dragonne Key Holder Cream/Saffron in Empreinte Leather with Gold-tone - US
Buy It Now 18d 17h


